Monday, April 22, 2024
Business

Common Mistakes in Professional Presentations and How To Avoid Them
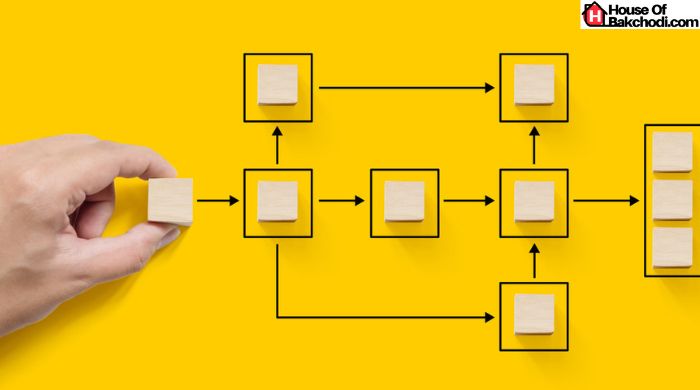
In a professional environment, the ability to make a compelling presentation is vital. It can position you as a leader,
Technology
![How to Unblock Skype in UAE? [Easy Guide for Seamless Calls] How to Unblock Skype in UAE](https://www.houseofbakchodi.com/wp-content/uploads/2018/01/How-to-Unblock-Skype-in-UAE-390x205.jpg)
How to Unblock Skype in UAE? [Easy Guide for Seamless Calls]
The United Arab Emirates (UAE) is one of the few countries in the world where Skype is blocked. This restriction
Entertainment

Mp4moviez 2020 : Download Latest Bollywood, Hollywood Movies on Mp4moviez.in
[su_button url=”https://t.me/latest_movies_download_free” target=”blank” style=”3d” size=”7″ wide=”yes” center=”yes” radius=”round” icon=”icon: telegram”]Join Our Telegram Channel[/su_button] Mp4moviez 2020: Mp4moviez is one of the
Fashion
World News
Travel

Agoura Hills: Everything You Need to Know About This Amazing Destination
Agoura Hills is located in Los Angeles County. It is the perfect destination for those who enjoy travelling. Its population


![How Combination Charts Are Applied In Business? [Detailed Guide] How Combination Charts Are Applied In Business](https://www.houseofbakchodi.com/wp-content/uploads/2023/11/How-Combination-Charts-Are-Applied-In-Business.jpg)

![How Combination Charts Are Applied In Business? [Detailed Guide] How Combination Charts Are Applied In Business](https://www.houseofbakchodi.com/wp-content/uploads/2023/11/How-Combination-Charts-Are-Applied-In-Business-392x272.jpg)

![How Combination Charts Are Applied In Business? [Detailed Guide] How Combination Charts Are Applied In Business](https://www.houseofbakchodi.com/wp-content/uploads/2023/11/How-Combination-Charts-Are-Applied-In-Business-130x90.jpg)




![5 Best Personal Website Builders [Must Try Platforms] Best Personal Website Builders](https://www.houseofbakchodi.com/wp-content/uploads/2022/07/Best-Personal-Website-Builders-130x90.jpg)




